Classifying an industrial system is a first step; making that classification operational in the field is another matter altogether.
This is precisely where version 2.0 of the guide “Industrial Systems Cybersecurity – Detailed Measures”, published on November 27, 2025, positions itself: translating cybersecurity classes into concrete measures, at a time when OT environments must contend with a more acute threat landscape, increasingly interconnected architectures, and more visible compliance requirements.
This guide directly follows the publication of the second version of ANSSI’s Industrial Systems Classification Method in March 2025, which we had already analyzed in a previous article.
An update built on continuity: the same structure, the same underlying logic
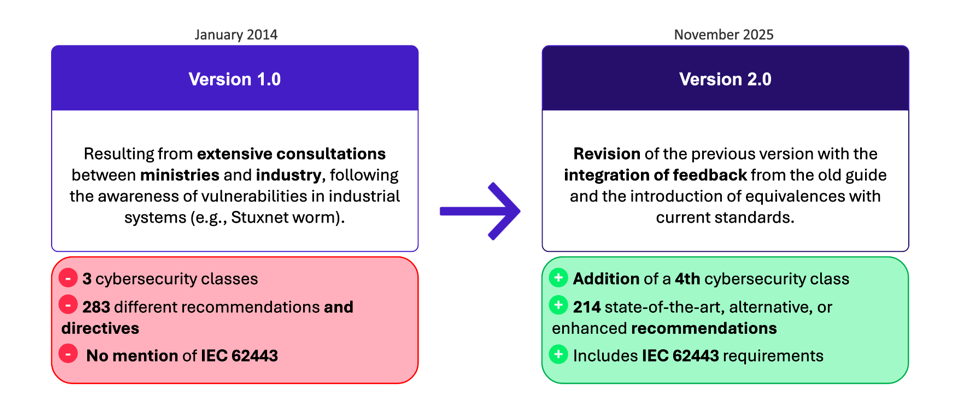 Key differences between the first and second versions of the detailed measures guide
Key differences between the first and second versions of the detailed measures guide
In terms of structure, the 2025 guide remains very close to the 2014 version. It opens with a reminder of the constraints and weaknesses specific to industrial environments, followed by a clear separation between organizational and technical measures. The themes themselves will come as no surprise: governance, access control, network segmentation, remote access, backups, supervision, vulnerability management, cybersecurity integration throughout the system lifecycle, and incident preparedness. Continuity is clearly intentional.
This stability has an advantage: organizations already aligned with the 2014 guide do not have to start from scratch. At the same time, it also highlights the fact that most of the “core topics” were already well identified more than a decade ago. The real question is therefore less “what is new?” than “what has become more actionable — and at what cost?”.
On this point, the guide is explicit about its scope. It proposes a minimum baseline intended, among other things, to support security accreditation processes. However, it does not claim to replace IEC 62443, nor does it position itself as a certification framework. It simply reuses some of its principles and requirements, while clearly stating that the measures alone are not sufficient for the most critical systems.
What has changed in concrete terms
The most visible change is not the introduction of new topics, but a new way of expressing requirements.
In 2014, the guide relied on a structuring distinction between recommendations (R) and directives (D), with a hardening mechanism depending on the cybersecurity class. In 2025, this grammar disappears. The guide now introduces a class based reading (C1 to C4) and several variants:
– state of the art recommendations,
– lower level alternatives, indicated by a “–”,
– and reinforced complementary recommendations, indicated by a “+”.
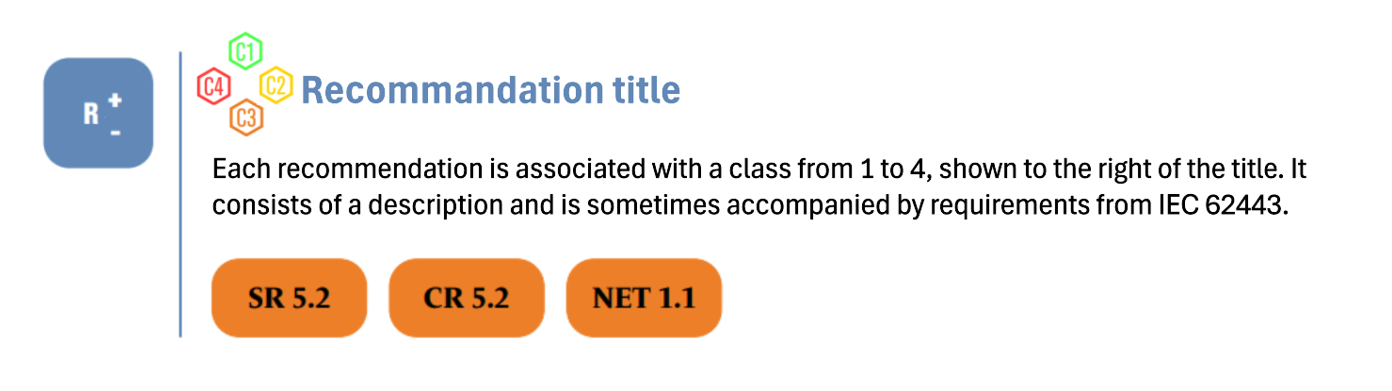 Typical structure of a recommendation
Typical structure of a recommendation
A second major evolution is the explicit introduction of a fourth cybersecurity class and the strengthened alignment with IEC 62443, in line with the updated classification method. For each recommendation, a correspondence with an IEC 62443 requirement is indicated when it exists and referenced in a dedicated appendix.
According to Appendix B, a large proportion of the 214 recommendations have a direct equivalent in the previous version. This confirms that the overhaul is primarily based on reorganization and reformulation rather than a fundamental shift in doctrine. After analyzing the 35 measures identified as having no direct equivalence, it appears that they are not necessarily new. They typically reflect:
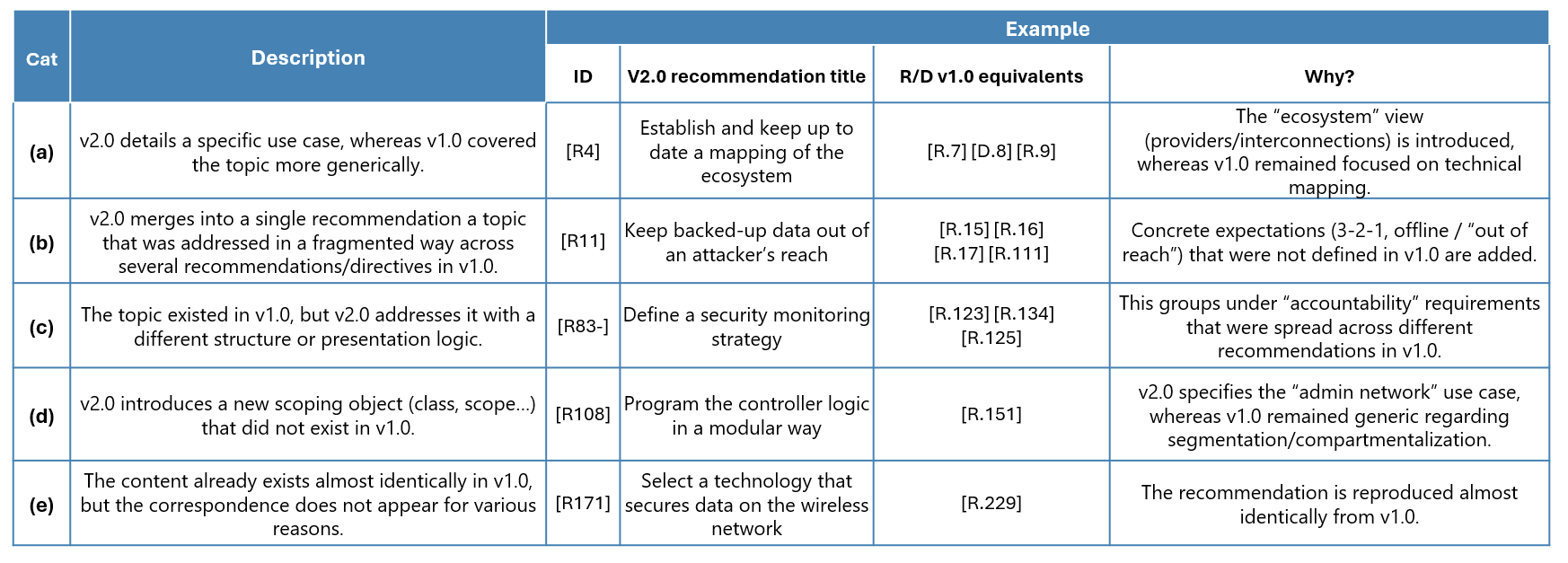 Categories of reasons for no direct equivalence, with illustrated examples
Categories of reasons for no direct equivalence, with illustrated examples
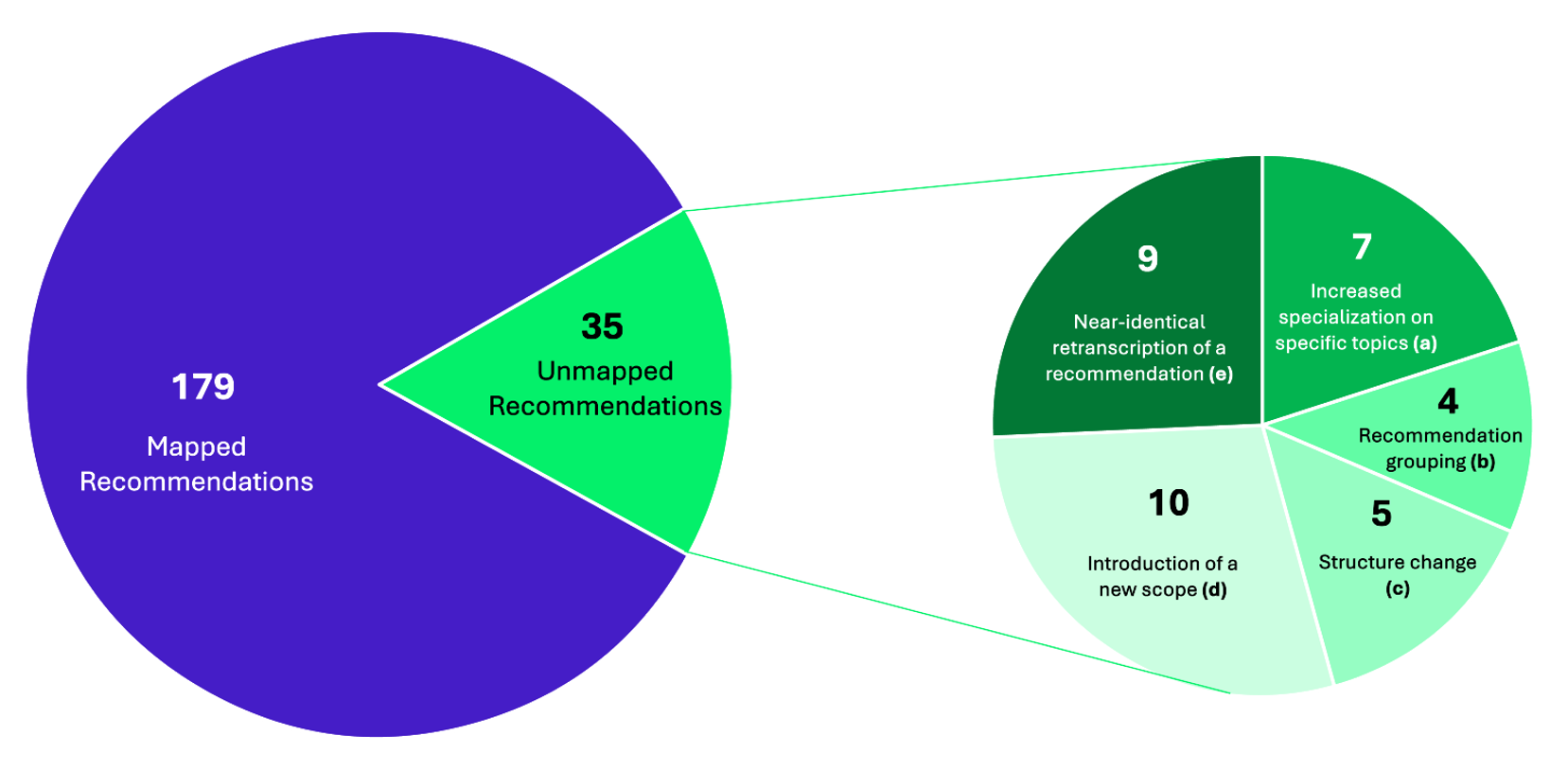
Summary of recommendations with no direct equivalents in Annex B
A more architecture-driven doctrine on interconnections and remote access
Where the 2025 version truly changes the dynamic is in certain topics that are handled in a more structured way. In the first version, the doctrine on interconnections and remote access was already relatively prescriptive: it emphasized that remote management greatly increases the attack surface, set out operational rules, and even went as far as banning remote maintenance in class 3, using a logic of one-way (unidirectional) data flows.
The modernization brought by the 2025 version makes the whole set more coherent and better structured: it moves from a reasoning mainly centered on components and means (firewalls, VLANs, data diodes, VPNs) to an interpretation in terms of security functions that must be combined and positioned according to the classes and the flow directions in Table 3. The rows of the latter correspond to the issuing class (“from”) and the columns to the receiving class (“to”); the icons indicate the security functions to implement in order to authorize the flow in that direction. For example, from class C1 to IT, only a system that can verify whether the data comes from an authorized source—Aut(IT)—is required.
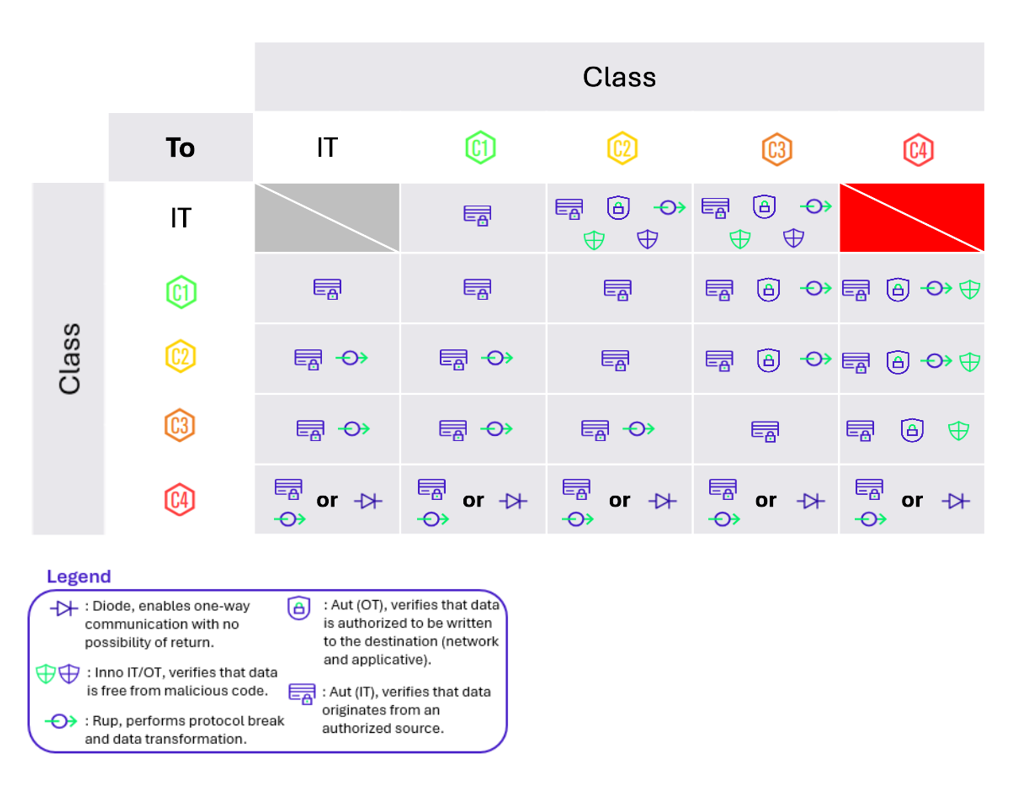
Summary of Table 3 – Section 4.2.1: all listed measures are associated with a data transfer unidirectionality function
It should be noted, however, that the definition of Inno (OT) is not explicitly provided in the document.
From framework to on-the-ground implementation
The 2025 version of the Detailed Measures logically brings to a close the overhaul initiated with the publication of the second version of the classification method, and it strengthens compatibility with IEC 62443. In a context where the threat to industrial environments is now highly visible, this document comes at just the right time: it’s an opportunity to adjust your action plan—or even to launch a full 2030 roadmap. A guide that isn’t put into practice has never stopped an attacker!
Among the priority workstreams that are regularly identified, we often see:
- Revisit the IT mapping and the business’s dependencies on IT
- Adapt the technical architecture by trading “new authorizations” for stronger authentication and better content control
- Harden and centralize remote access, especially given the many suppliers present in industrial environments
- Strengthen industrial environments or connect them to your SOC


