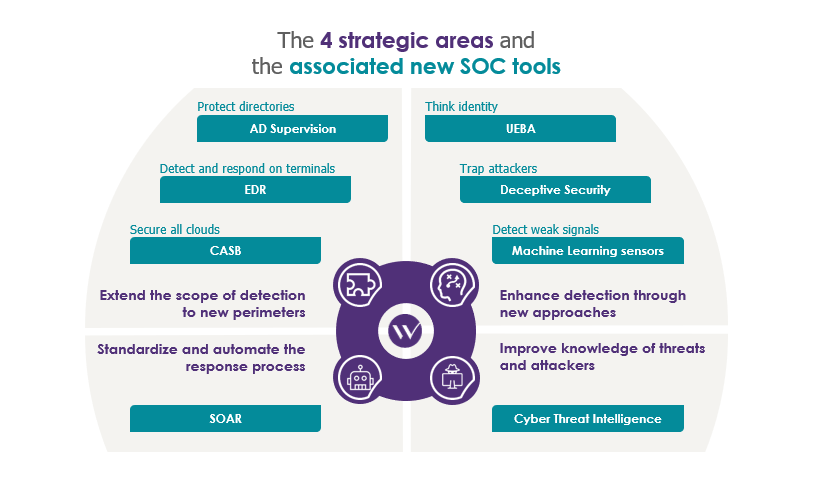
After the first article which covered “Extending the scope of detection to new perimeters” (see here), and the second, dedicated to “Enhancing detection through new approaches” (available here)… this is the conclusion to this (epic!) saga. This last installment will cover the last two strategic areas.
Improving knowledge of threats and attackers
Cyber-threat intelligence (CTI) platforms
Cyber-Threat Intelligence (CTI or Threat Intel) is a discipline that brings together the collection, consolidation, and exploitation of all information on cyber-threats. “Know your enemy” says Sun Tzu in the Art of War. Although this quote refers to “physical” wars, the principle remains true, and is probably even more true when it comes to “cyber” battles.
Today, a large number of security approaches rely on knowledge of attacks: the signature-based approach of antivirus and IDS solutions, targeted detection scenarios, etc. Even though this trend is reversing (in particular with the detection of anomalies) the vast majority of security products still rely—and will continue to rely—on the principles of Threat Intelligence.
With companies’ needs becoming more specific, and attackers ever more specialized, Threat Intel solutions are becoming increasingly popular, with services being offered directly to companies. In addition to commercial offerings, more and more exchange platforms and partnerships are enabling direct collaboration with other companies (in the same sector or geographical area, etc.).
Threat Intel offers a range of services. On the one hand, ‘strategic’ Threat Intel helps an SOC better understand the context and specific threats to the company. To do this, the risks from various ecosystems are studied: geographical, political, ideological, sectoral, etc. This information enables security teams to better understand the threats they face and guides their decisions to define “long-term” strategy (solutions to be deployed, etc.).
On the other hand, ‘tactical’ Threat Intel provides more precise information on attackers’ methods, allowing the SOC to facilitate detection and tailor existing measures: new threat scenarios to monitor, ports to block, etc.
In addition to these approaches, ‘technical’ Threat Intel contributes greatly to the analysis of security events by providing, on request (from SOAR in particular—see below), elements that enable the veracity of an alert to be judged: an IP belonging to a botnet, a file hash corresponding to a known virus, etc.
Threat Intelligence approaches are therefore among an SOC’s most versatile tools, enabling it to make the most of existing devices, by remaining up to date and prioritizing the threats to be detected, as well as identifying future tools and measures to be deployed.
Examples of Threat Intelligence publishers:

The standardization and automation of the response process
Security Orchestration, Automation and Response
Security Orchestration, Automation and Response (SOAR) is derived from the combination of three SOC tools: Security Incident Response Platforms (SIRPs—more details here), Security Orchestration Automation (SOA— orchestration and automation solutions) and some of the functionality of Threat Intelligence platforms. In summary, these are platforms that provide help and automate responses to security incidents. The solutions are similar to traditional ticketing tools (ITSMs) but include functionalities specific to cybersecurity issues. SOARs offer three main capabilities, each linked to one of the three types of tools from which they are derived.
First, like SIRPs, they allow the definition of response processes that are tailored to each security event. These are based on pre-defined playbooks provided by the publisher, published by the community using the solution, or created manually to better tailor things to the needs of the business. In particular, this task requires response teams to establish a clearly defined process that encourages them to ask themselves the right questions when they create response procedures, as well as to capitalize on and retain the knowledge gained.
The benefits of a SOAR, however, come more from the automation of the various stages that follow detection. During the analysis phase, the tool will automatically enrich knowledge about a security event by retrieving contextual information about the IS (identity in the AD, criticality of a resource, etc.), and querying external Threat Intelligence services (via APIs) or those that are offered as part of the solution. In addition to automating the enrichment and analysis steps, SOARs also facilitate the work of analysts: the investigation of terminals, the interrogation of VirusTotal etc. in one click—when their involvement is required.
But automation doesn’t stop there! Although controversial, the automation of the response (via the connection to security equipment, a legacy of SOA) can represent an important gain for security teams: the blocking of a URL, the generation of the signature of a file and its propagation to antivirus tools, the blacklisting of an IP, etc.
The goal of SOARs is clear: to make it easier for the teams in charge of analysis and response, by helping them to define processes and automate tasks to the greatest extent possible. Although SOARs are very adaptable and can therefore help in response to any type of attack, they really shine when it comes to automating the treatment of common attacks (such as ransomware, phishing, etc.), which are very repetitive and tie up the resources of response teams.
Once these tasks have been automated, the security teams responsible for responding can focus on more complex alerts, where their knowledge adds real value.
Provided they are prepared to put in the initial effort (the formalization of processes, etc.), the likely reactivity and load gains are significant. SOARs will change the way SOC teams work, especially with respect to top-level analysts. Even though these solutions are still rarely deployed in France, they are set to become an essential tool for SOCs in the coming years.
Examples of SOAR publishers:

Even though tools are only part of equipping an SOC, each of these solutions has distinct advantages that can help detection teams keep up to date in terms of the evolution of ISs and threats.
All the tools are promising, and some are coming to maturity. However, it’s important to keep in mind that current toolkits already raise a raft of alerts, which presents a challenge when it comes to processing. It’s therefore advisable to complete the deployment and automation of what exists (using SOARs, for example), before turning toward new solutions.
And, as for any innovative product, a cool head is needed: the deployment of a new solution must be the result of well-defined needs.


