The cybersecurity topic requires involvement at all levels of the company, but also and above all with the executive committee! Obviously, management must be an example, but it will also decide on major investments and will know how to unlock the most complex situations in the company. It is therefore a key issue for all cybersecurity managers to create a lasting relationship of trust with their EXCOM. But it is also a high-risk exercise, which requires a gradual approach and consistency in commitments.
After having made several dozen speeches to executive committees, audit committees and boards of directors, I wanted to share with you the essential steps for advancing the relationship over the long term. The first phase of this trip should make it possible to create an initial contact and raise the EXCOM’s awareness on cybersecurity issues. First step, awareness! The objective for these sessions is often to manage to attract attention so as to be able to trigger further reflection within the organization. Later on, we will see the following steps: presenting a balance sheet, obtaining a budget, monitoring the progress on the security level…
An essential prerequisite, knowing where you are starting from and who you are going to deal with
This may seem like a cliché, but it is certainly the most important element before going to meet an executive committee or a board of directors. Thanks to its wide media coverage, cybersecurity is often already present in executives’ minds. But their degree of digital literacy and their level of appetite for the topic can completely change the way the topic is raised. Will it be necessary to be very didactic (going so far as to re-explain the principle of data, applications, if any) or will it be necessary to immediately address complex points such as the latest attacks observed and their methodologies? You would be surprised to see the diversity of levels between companies, but also within the same EXCOM. And it is necessary to interest each of the stakeholders, at the cost of having comments that are not very helpful during the intervention.
It is therefore important to prepare this first meeting by talking with other members of the ECOM their deputies or with people familiar with this forum to determine the tone to be adopted and the level of the speech to be given. Obviously, the operating rules will also have to be known: is it common for questions to be asked as they arise? Can a member be questioned? Should subjects relating to the company be raised from the outset? Plan to clear the ground upstream! And even if there is no perfect recipe, I will give you below the elements I use most often to make these meetings useful and effective.
To start, draw the attention by revealing the behind-the-scenes of an attack…
The topics quickly follow one another during the EXCOM. The directors think very, very quickly, so it is necessary to be concrete and to give food for thought and experience. The element that I find most effective consists in presenting a recent attack, published in the press or having affected the sector, and deciphering the stakes and the background: what is the timeframe? what motivation for the attackers? what weaknesses in the company? what is the reaction internally? publicly? with the authorities? This will have the effect of mentally projecting the directors concerned into their role as if they were going through the same thing. We at Wavestone are fortunate enough to frequently manage major cyber crises and we use these elements, both as a benchmark but also by anonymizing them or in agreement with the victims, to give a very concrete meaning to our feedback.
Follow-up with a generalization about cybercrime
An case is good to understand, but it doesn’t explain everything! After zooming in on a case, it is a question of generalizing it by explaining what are the mainsprings cybercriminality ways of proceeding. We then analyze the motivations of criminal groups, their organizations, but also and perhaps above all how they make money!

For an EXCOM to know that it is a DDoS attack or ransomware that has done damage is of little interest, it is especially important to show them that cybercriminal activities are profitable, even very profitable. We have calculated the ROI of several types of attacks and I can tell you that when you explain a 600% profitable attack like a ransomware, the eyes of the directors are wide open. We then highlight very concretely why their structure could be attacked and especially how much money the criminals would make. This often puts an end to the question “but why would we be targeted by an attack? We’re not known/we’re small/we don’t do anything strategic”.
Explain the company’s current situation in concrete terms
This is the right time to present the company’s IT posture and its current organization in terms of security. It is then a question of presenting it simply, with clear and meaningful images: are you rather in an old-fashioned “fortress” model? Or have you already opened your doors as a result of the digital transformation and have you adopted a porch model where security is reinforced the further you go towards critical systems? This will help to make the situation more concrete.
After this phase of mobilization and explanation, comes naturally the phase of questioning by the members of the executive committee. “But then, where are we now, or are we facing this risk of a cyberattack? ». Faced with this question, either you are lucky enough to have a detailed maturity assessment and you can present it immediately, or you can bring in initial qualitative or even partial quantitative elements and explain that today you need to have more visibility. The elements that speak for themselves are the latest audit reports, the latest incidents, budgetary elements.
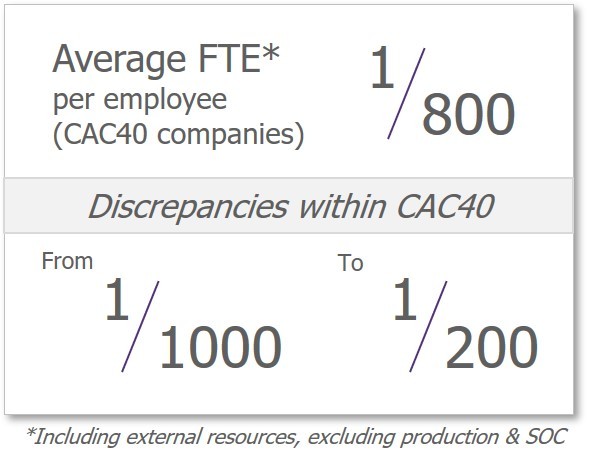
If it is difficult at the beginning of the process to talk about the budget and to compare oneself because of a lack of data, it is possible to use a simple and effective indicator, that of your staff dedicated to cybersecurity. We have a database on this point and we can quickly show a EXCOM where it is just by mobilizing its HR. It’s simple and effective to convince them!
Don’t leave emprty-handed
The major risk of this awareness is that everything goes well but nothing moves. Indeed, you may have a positive message, “thank you and see you in a year for an update”, you will be happy but you will not have helped cybersecurity situation moving forward. It is then necessary to prepare the next step by indicating from this presentation the main points of weakness or strength felt and how you would like to evaluate them more precisely.
Indeed, the second step is often the realization of a dedicated maturity assessment in order to know how to position yourself! If at this point the meeting has taken place, the EXCOM, intrigued and interested in the topic, will want to know more and will give an agreement in principle. Beware that this may not be a budget directly, it will certainly refer you to the CIO or the Risk Director to get it, but with their agreement you will have a great lever to move on to the next step! See you on the next episode.


