Subscription hijacking is a cloud attack first identified on Microsoft Azure: it consists of an attacker successfully transferring an Azure subscription from its original Azure organization to an organization under malicious control. This attack allows the attacker to take full…
Tag: risk management
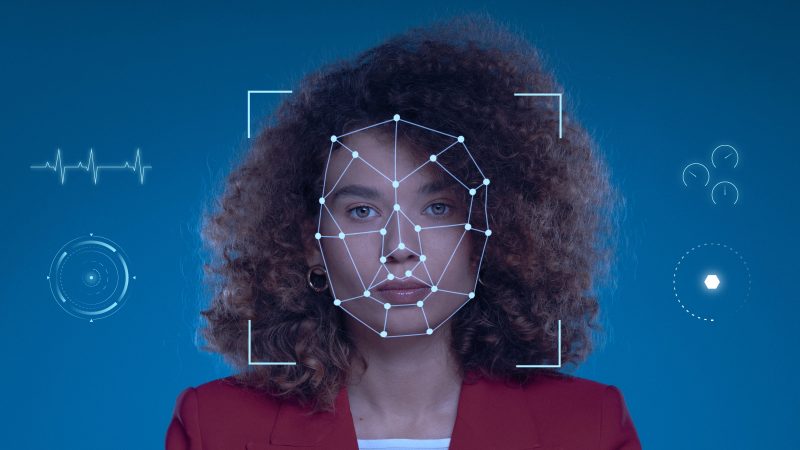
A deepfake is a form of synthetic content that emerged in 2017, leveraging artificial intelligence to create or manipulate text, images, videos, and audio with high realism. Initially, these technologies were used for entertainment or as demonstrations of future capabilities. However, their malicious misuse now…
Since the massive rise of DevOps, continuous integration and deployment (CI/CD) pipelines have become essential to automate application development cycles. Continuous Integration (CI) involves merging and testing code automatically, while Continuous Deployment (CD) automates the entire process of releasing that…
The UK insurance and reinsurance industry is navigating a period of rapid transformation, marked by regulatory reform, accelerating cyber threats, and shifting macroeconomic conditions. With a combined market valuation of £74.6 billion and forecasted earnings growth of 18% annually, the…
While AI has proven to be highly effective at increasing productivity in business environments, the next step in its evolution involves enhancing its autonomy and enabling it to perform actions independently. To this end, one notable development in the AI…
What if your most sensitive data became accessible in an instant? The growing excitement about the advent of quantum computers is justified for a subject that is no longer science fiction but involves a new kind of threat. Indeed, according…
This article was originally published on our corporate website wavestone.com on 26 January 2023. Cybersecurity awareness is a journey to embed secure behaviours in people's daily lives To do so, you need to build a strong cyberawareness program, focus…
Not familiar with CMMC 2.0? For more information regarding CMMC 2.0, please refer to this article. The Cybersecurity Maturity Model Certification (CMMC) is a comprehensive framework designed to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI), shared with…
In late October 2023, a third-party data breach incident sent shockwaves through the business world, affecting over 57,000 entities engaged in business with Bank of America. This breach exposed sensitive personal and financial information, underscoring the pivotal role that third-party…
We have recently opened the contributions to this blog to start-ups accelerated by our Shake'Up project. Hackuity rethinks vulnerability management with a platform that collects, standardizes and orchestrates automated and manual security assessment practices and enriches them with Cyber Threat…