CERT-Wavestone handles cybersecurity incidents of all types and magnitudes, from investigating a single suspicious workstation to large-scale overnight ransomware outbreaks. After 10 years of forensics investigations and crisis management at Wavestone, one thing stands out: attackers are more sophisticated than ever, and every hour matters for blue teams.
When CERT-Wavestone is called, three priorities drive every action and decision making: containing the threat, understanding the attack and eradicating the attacker. To achieve these objectives, establishing visibility across the impacted perimeter is the critical first step.
In such contexts where speed and effectiveness are mandatory, CERT-Wavestone relies on many tools: cybersecurity solutions (EDR, SIEM, etc.), open-source collectors and parsers, and its own internally developed tools.
Among these, StormCell stands out as an open-source tool developed by CERT-Wavestone to automate Windows triage processing and free analysts’ time to focus on what truly matters: the investigation itself.
Contain. Understand. Eradicate. Every hour counts.
Increasingly effective attackers
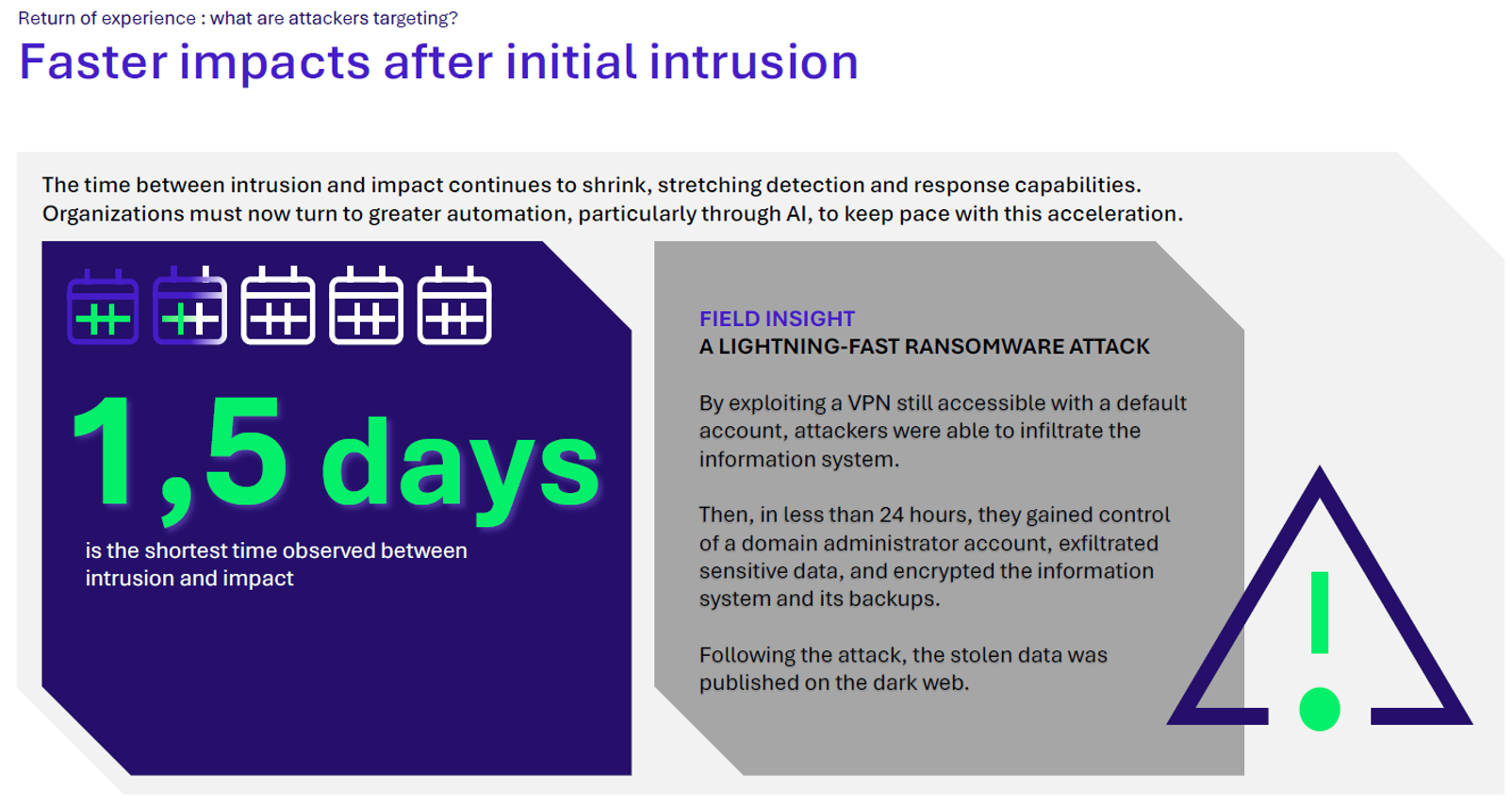
Several cybersecurity incident response actors agree that certain types of cyberattacks, such as ransomware and data exfiltration attacks, are becoming increasingly fast paced. The charts published by Zero Day Clock (https://zerodayclock.com) illustrate this trend:
- A growing share of zero day vulnerabilities are being actively exploited each year, rising from 16% in 2018 to 71% in 2026,
- A decreasing time to exploit (TTE) for these vulnerabilities is noted, falling from several years in 2018 to less than one day in 2026.
This is also a commonly shared observation among Wavestone’s incident response team in its latest annual report (see: CERT-Wavestone annual report), which is based on a set of around twenty major incidents affecting Wavestone clients during 2025:
As a result, to contain and remediate incidents as early as possible our incident response team must be effective in its analysis and decision‑making. This requires an especially quick understanding of the context and of the incident.
The anatomy of a CERT-Wavestone investigation
Each CERT-Wavestone investigation typically begins with a limited scope before rapidly expanding to cover dozens of systems as the situation evolves:
- Stage 1 — Initial analysis: Once the perimeter is secured and initial containment measures are in place, CERT-Wavestone is engaged and assesses the situation on a handful of suspicious or confirmed compromised machines. If the client has a SOC or CERT, existing telemetry and detection tooling provide an immediate starting point. If not, CERT-Wavestone leverages available resources to perform initial forensic collections and outline an initial overview of the attack.
- Stage 2 — Broader investigation: As the killchain becomes clearer, the investigation expands to dozens of compromised machines. When the client’s infrastructure cannot support large-scale acquisitions, CERT-Wavestone deploys its own forensic collection tool to gather triage data efficiently.
- Stage 3 — IoC hunting across the entire IS: Indicators of compromise are established, and the search extends to the entire information system. If not already in place, EDR or alternative tools can be deployed by CERT-Wavestone. Large-scale IoC sweeps rely on the built-in capabilities of the EDR, SIEM or log collection platforms.
Whether on Stage 1 or Stage 2, each collection requires the same standardized pipeline: retrieval, parsing, ingestion, Indicator of Compromise (IoC) identification, and cross-collection correlation. Consequently, manual forensic processing consumes valuable time and effort, forcing analysts to handle routine data operations instead of focusing on investigations.
Handling each collection individually by each analyst is slow, prone to errors and discrepancies, and poorly scales to the number of machines to investigate, and the number of analysts mobilized on the incident.
This is precisely the problem that StormCell, a tool developed by the CERT-W, was designed to solve.
StormCell : what is it ?
StormCell is a tool developed by CERT-Wavestone to address a long-standing need: a Windows forensic analysis orchestrator that adapts to multiple investigation contexts, automates the end-to-end processing of triage data from artifact extraction to centralized ingestion into a SIEM platform, and frees analysts to focus on the investigation, not the pipeline.
Developed in Python to make it easy to use, the tool was recently published on GitHub so that the entire incident response community can access it as open source: https://github.com/CERT-W/StormCell. CERT‑Wavestone intends for this tool to be used, tested, and improved directly by the community.
Although other similar tools have been developed and released since the beginning of its development, StormCell stands out through its modularity and its underlying technology choices, both geared towards speed and adaptability.
Three key stages : ingest, process and enrich, centralize
StormCell’s workflow is based on three key stages:

To properly perform those steps, StormCell relies on several third-party tools : whether it is for artifacts collection with Kape, enrichment and ingestion of logs into a SIEM with Vector or SIEM built-in functionalities with Splunk or ELK.
Despite these dependencies, the tool only needs to be installed and configured once on a single workstation before it can be used throughout the incident response by all analysts.
Extract and Ingest
StormCell is designed to work with two types of forensics collections: disk images and artifact ZIP extracts produced by Kape.
When StormCell is run against a disk image, it directly uses Kape to extract the relevant artifacts.
Compatible ZIP archives can also be generated with the CERT‑Wavestone tool CollectRaptor, which is based on Velociraptor, or with any other collection performed using the Velociraptor KapeTarget module.
Process and Enrich
Once raw artifacts are extracted, the core of the processing chain comes into play: the artifacts are processed with Kape.
Kape is used because it is a tool dedicated to Windows forensics artifacts parsing. It allows, through modules, to automatically execute several tools such as the Zimmerman Suite, Hayabusa or even Chainsaw. Moreover, logs parsed by Kape are directly organized on the filesystem by artifact category (executions, filesystem, registries, etc.) allowing to perform efficient local and manual analysis whenever necessary.
As a whole, StormCell uses Kape to run more than thirty artifact‑processing tools, each covering a complementary analysis scope and ensuring a high level of exhaustiveness for the elements available to analysts.
All these tools can be easily downloaded through the StormCell installation command described in its Readme. StormCell’s modular configuration also makes it simple to integrate new artifact‑processing tools as needed.
Centralize
Once the artifacts have been parsed by Kape, the generated logs are normalized, enriched, and sent to a SIEM platform through Vector, an open‑source tool particularly well‑suited to handling large volumes of data.
To determine which artifacts to send, as well as the normalizations and enrichments to apply, Vector relies on its TOML configuration files. These files include parsers that structure raw data into meaningful fields, and sinks (output destinations) that route events to the target environment, whether a client’s ELK or Splunk instance, or an internal ELK instance dedicated to CERT‑Wavestone.
To retrieve these configurations, StormCell uses the configuration files from the GitHub repository Vector4IR whose CERT‑Wavestone is a contributor.
A major time-saver for analysts
By chaining these three stages together, each forensic collection only needs to be processed once before it becomes available in the SIEM for all analysts. This makes it possible to carry out global investigations while fully leveraging the built‑in capabilities of SIEM technologies: search languages, dashboards and saved searches, lookups and data tables, correlation features, and so on.
The retrieval of collections and their handling with StormCell can be handled by a single analyst, while the others can already begin investigating in real time as the logs are being sent.
StormCell execution modes
According to the setup and configuration details provided in the Readme of the Github repository, a dedicated setup command can be used to download all the tools required for StormCell to properly operate. In addition, numerous options, described in the default configuration file and the help command, are available to accommodate different execution requirements.
For example, it is possible to specify which Kape modules should run, or to force a fresh processing and re‑ingestion of logs. Because StormCell uses a local database file to maintain state across successive executions, its behavior can be completely reset by removing this database.
Finally, StormCell offers three complementary execution modes, designed to adapt to every investigation context, from small scopes to large‑scale crises, and to let analysts be operational as quickly as possible, regardless of the types of resources available to them.
Once mode: small scopes and need for rapid investigation
Designed specifically for targeted investigations on a limited scope, this mode handles a set of preexisting collections in a single execution.
After an initial configuration by the analysts, the tool executes and enables the analysis of the collections without any additional steps.
Mountpoint mode: local collect and analysis in a single command
Mountpoint is StormCell’s end‑to‑end execution mode: from collecting artifacts on a disk or a locally mounted forensic copy all the way to sending them into the SIEM.
This mode is preferred when analyzing disk copies, and it natively includes artifact extraction through Kape’s built‑in capabilities. Once the extraction is complete, its behavior is similar to the Once mode.
Loop mode : Continuous processing for large‑scale investigations
CERT-Wavestone’s preferred mode, it is designed for large‑scale crises and aims to enable StormCell to run continuously throughout the incident. Once configured, the tool monitors a designated folder and automatically processes all collections placed there by the analysts.
This centralized drop‑off folder becomes the logistical core of the investigation: once it is set up, analysts no longer need to worry about processing collections, whether the incident lasts a few days or several weeks, and can simply deposit the triage images then access the processed data in the SIEM platform being used.
Finally, two levels of artifact processing can be configured to best match analysts’ needs when investigations are carried out on new machines:
- Short: a lightweight treatment prioritizing speed, suited to surface‑level analyses that quickly assess a machine and help prioritize investigations.
- Long: an exhaustive treatment that activates in‑depth analysis modules, intended for detailed investigations requiring a full view of the machine’s activity.
The modules to be executed in both modes can be freely configured by the analyst using StormCell. These two complementary modes make it possible to deposit archives initially into the Short folder to obtain a quick but non-exhaustive list of artifacts, then later in the investigations, deposit them into the Long folder to obtain an exhaustive list of artifacts.
StormCell : What’s next ?
StormCell is currently a key tool frequently used within CERT‑Wavestone to accelerate the processing of Windows artifacts during its investigations.
Its orchestration capabilities are planned to be extended to investigations on Cloud environments, particularly M365, as well as Linux and macOS, while also exploring the integration of new forensic sources and advanced technologies such as the use of AI.
That’s why CERT‑Wavestone invites you to contribute to its evolution: forks, pull requests, and feedback from your operational experience are welcome, so that StormCell can become the most suitable tool possible for incident response needs.


