The Quantum Threat Is Becoming Clearer
Quantum computing poses a serious threat to today’s asymmetric cryptography and is expected to render widely used algorithms such as RSA and ECC obsolete. By contrast, symmetric cryptography (such as AES) and hash functions, maintaining an equivalent level of security can be achieved by increasing key sizes or security parameters.
In response to this emerging risk, the NIST standardized four post-quantum asymmetric algorithms in August 2024, specifically designed to withstand attacks from quantum computers.
While quantum computers are not yet powerful enough to carry out such attacks, estimates vary as to when this capability will be reached, with many experts anticipating a timeframe between 2033 and 2037.
Nevertheless, the “Harvest Now, Decrypt Later” (HNDL) threat—where attackers collect encrypted data today with the intent of decrypting it in the future using quantum computers—makes it critical to protect sensitive, long-lived data well before such machines become operational.
2025: Regulatory Acceleration
While 2024 marked the completion of technical standards with the publication of the NIST specifications, 2025 stands out for the acceleration of institutional and regulatory roadmaps. In recent months, several major stakeholders have released their recommendations:
- The European Union has defined a roadmap for Member States and entities subject to NIS 2
- G7 Finance has formally integrated the post-quantum transition into its priorities
- The Bank for International Settlements (BIS) has raised awareness within the banking sector
- The UK government has published its national post-quantum roadmap
These announcements build on previously communicated timelines: the NIST released a draft targeting 2035, while the Australian Signals Directorate (ASD) set a 2030 deadline. We expect additional countries to issue similar announcements in the coming months.
As a result, the post-quantum transition is no longer solely a technological challenge. It is becoming a regulatory and institutional imperative, comparable to past largescale digital transformations. Regardless of the exact timeline for the emergence of quantum computers capable of breaking current cryptographic algorithms, a transition is unavoidable.
Migrating a complex IT infrastructure is far from trivial. According to a 2022 memorandum, the Biden administration estimated the cost of migrating all U.S. federal agencies at over $7 billion. Such a program spans multiple dimensions—from risk assessment to technical execution—and involves numerous intermediate steps. Dedicated solutions already exist to support and accelerate each phase of this transition.
The Wavestone Radar: A Market Overview of Solutions
The 2026 Wavestone Radar of post-quantum migration solutions provides a visual overview of the leading solutions available on the market to support this transition. It has been—and will continue to be—regularly updated and enriched over the coming months. Any company that believes it should be featured is encouraged to contact us.
The objective of this radar is not to list solutions that have already completed their post-quantum transition, but rather to highlight those that actively support and accelerate the migration process.
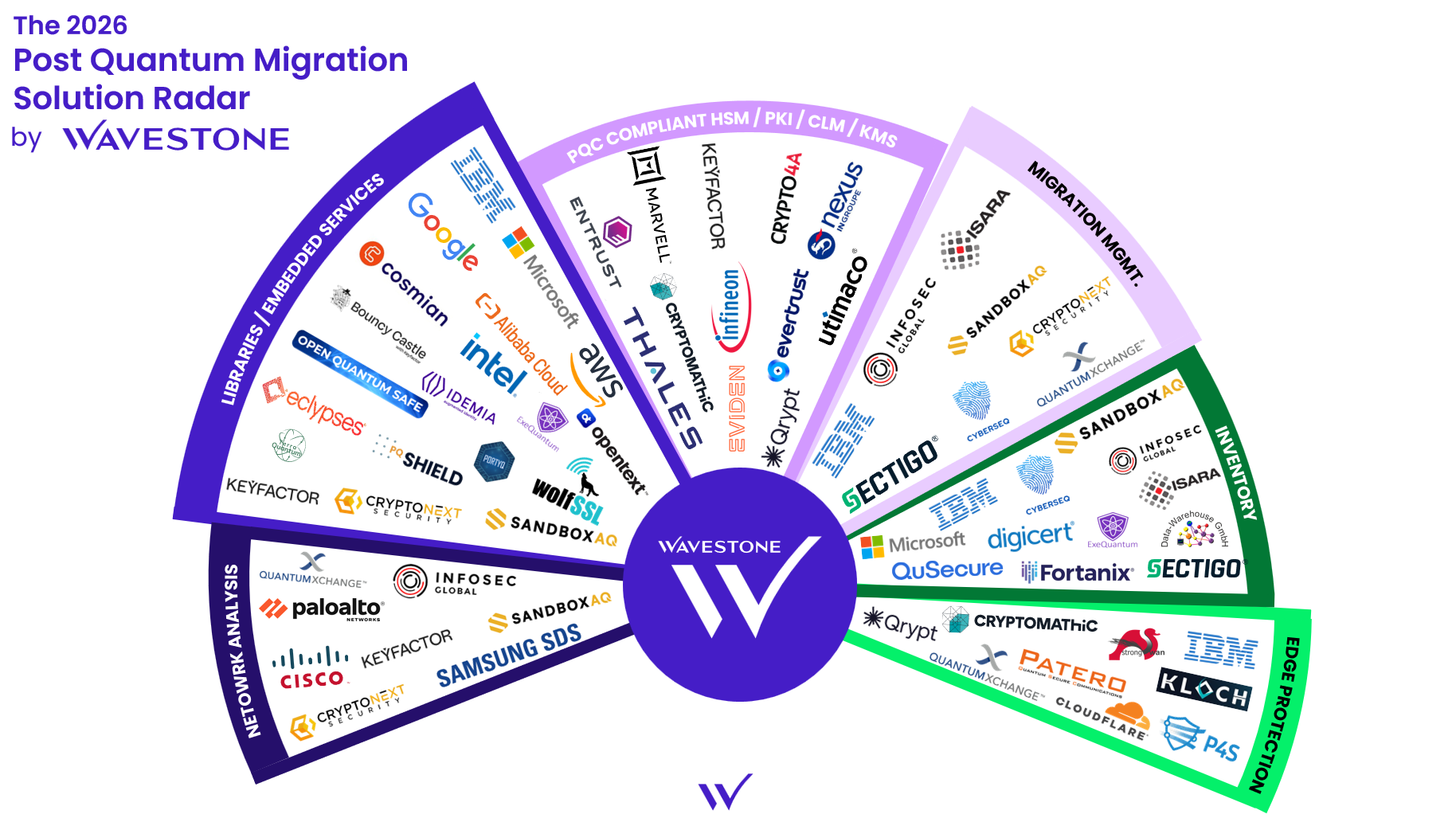
Radar Categories
Quantum Key Distribution (QKD) was considered but ultimately excluded as a category. While QKD is resistant to quantum computers, it is not technically a post-quantum cryptography technology and is not recommended by regulatory bodies.
- Inventory: Automating the identification of all cryptographic assets, including the types of cryptography used and their locations
- Network Analysis: Detecting network traffic that relies on obsolete cryptography using network probes
- Migration Management: Providing an end-to-end view of the post-quantum transition, often based on inventory or network analysis results
- PQC compliant HSM / PKI / CLM: Delivering essential digital trust components for most services that are resistant to quantum attacks
- Libraries / Embedded Services: Encrypting and signing data using versatile cryptographic libraries or cloud integrated solutions
- Perimeter Protection: Adding an additional layer of security against quantum threats, notably through traffic encapsulation and application wrappers for critical systems
Inventory: The Cornerstone of Any Migration
Our initial feedback from supporting post-quantum migration programs highlights a clear reality: it is impossible to plan and budget a migration without visibility into the existing environment. Concretely, organizations need to understand :
- Which use cases and data are involved?
- Where is cryptography used across the information system?
- Which algorithms are currently deployed?
Conducting an exhaustive inventory of a complex IT infrastructure represents a significant investment. It is therefore critical to prioritize the areas where inventory tools should be deployed first, based on three key criteria: data exposure (data accessible via the internet, exchanged with partners, etc.), long-term data sensitivity and vulnerability to HNDL attacks, and the technical components used to secure this data. Without this upfront visibility—understanding which algorithms are used, for which purposes, and to protect which data-effective migration planning becomes impossible.
However, cryptographic inventory cannot rely on a single source. Organizations must combine multiple complementary approaches: network probes enable real-time observation of traffic, code analysis identifies cryptographic usage within applications and internal developments, SaaS specific tools and interfaces with external providers reveal third-party dependencies, while existing CMDBs and reference repositories map the overall infrastructure. This multiplicity of sources creates a new strategic need for tools capable of centralizing heterogeneous information and providing a consolidated, actionable view to effectively manage migration. A trend is emerging around the CBOM (Cryptography Bill of Materials) format to standardize these inventories, although it is still too early to assess its actual adoption across the market.
Inventory thus becomes the foundation of post-quantum migration governance. Without it, organizations are effectively navigating blind.
Since 2024, the market for digital asset inventory solutions has experienced strong growth, driven by the emergence of highly specialized players focused exclusively on the detection, mapping, and management of IT assets (hardware, software, cryptographic certificates, etc.). These vendors stand out for their deep expertise and ability to address complex environments.
At the same time, established players in the network and infrastructure space – such as IBM, Samsung, Cisco, and Microsoft – are leveraging their deep knowledge of IT environments to deliver robust solutions. These offerings increasingly integrate advanced network probes and cryptographic inventory capabilities, with growing attention paid to post-quantum cryptography challenges.
CryptoAgility: A Long Term Objective of the Post-quantum Transition
Cryptoagility is not merely a technical feature; it is a strategic capability that enables organizations to adapt to cryptographic evolutions without operational disruption. As post-quantum cryptographic (PQC) algorithms increasingly become a regulatory standard, cryptoagility allows business logic to be decoupled from the underlying cryptography, thereby facilitating updates without requiring a complete overhaul of existing infrastructures.
To adopt a crypto agile approach, organizations must embed flexible and scalable mechanisms from the design phase, capable of adapting to cryptographic advances—whether driven by the quantum threat or by the rapid deprecation of algorithms.
On the library side, solutions offering a modular approach are now widely available. Tools such as Open Quantum Safe (OQS), compatible with OpenSSL and BoringSSL, or liboqs (Intel), optimized for x86 architectures, enable the integration of NIST standardized post-quantum algorithms (Kyber, Dilithium, SPHINCS+). Bouncy Castle, for its part, provides a unified API for Java and C#, easing the transition between classical and post-quantum cryptography.
However, the modular approach offered by these libraries must be integrated into a broader ecosystem of specialized tools. In this context, inventory solutions and cryptographic key and certificate lifecycle management tools play a critical role. They enable the establishment of an exhaustive mapping of the cryptographic environment, providing full visibility into all assets that need to be protected. This comprehensive view forms an essential foundation for ensuring data security and implementing truly effective risk management.
Ultimately, crypto agility goes beyond the technical domain. It is a strategic capability that allows organizations to secure their data sustainably, reduce quantum related risks, and approach the future with greater confidence. The technological building blocks are already in place; what remains is to integrate them today into cybersecurity strategies.
Perimeter Protection: A Rapid Mitigation Strategy
Given the scale and complexity of post-quantum migration programs, perimeter protection (edge protection) solutions provide a pragmatic and fast acting approach to reducing exposure across critical data flows.
These solutions enable the rapid securing of sensitive communication channels—such as VPNs, email, and file transfers – by encapsulating traffic within a post-quantum cryptographic layer, without requiring changes to the underlying applications. This makes it possible to deploy wrappers around critical applications without waiting for their full redesign or migration.
The primary advantage of this approach lies in the significant time savings it delivers. While a comprehensive application-level migration remains necessary in the medium term and may span several years, perimeter protection offers immediate security for the most exposed assets. This strategy allows organizations to intelligently prioritize the protection of their most sensitive data, while methodically preparing for the broader, long-term migration of their IT infrastructure.
HSMs and Certifications: A Turning Point in 2025
In the first version of our radar, we highlighted the lack of certifications for post-quantum Hardware Security Modules (HSMs), which represented a major barrier to their deployment in production environments.
This situation has since evolved positively. Both the ANSSI and the BSI have now issued three Common Criteria certifications for PQC compatible HSMs (from Samsung, Thales, and Infineon). These certifications mark a significant turning point and pave the way for real-world deployments under operational conditions.
HSMs play a critical role in the digital trust chain, particularly for:
- The secure generation and storage of PQC keys, which are significantly larger than their classical counterparts
- Signature operations within Public Key Infrastructures (PKIs)
- End-to-end key lifecycle management (rotation, revocation, archiving), ensuring integrity and traceability to maintain the chain of trust
However, even when certified, these HSMs must still address challenges related to side channel attacks, given the relative immaturity of current implementations of these new algorithms. The scientific community continues to actively assess and analyze these risks.
IoT and Embedded Systems: The Weak Link
While the market for PQC solutions is progressing rapidly for traditional IT environments, a worrying gap is emerging for IoT and embedded systems. These devices operate under severe constraints – limited power, reduced processing capabilities, and restricted storage – which directly conflict with the requirements of post-quantum algorithms, inherently more resource intensive than their classical counterparts.
Deploying PQC on such systems often requires dedicated processors with optimized instruction sets. However, the current hardware ecosystem remains insufficient: few dedicated PQC hardware accelerators are available on the market, and hardware development cycles typically span several years. This technical complexity is compounded by the challenge of upgrading a highly decentralized and heterogeneous device landscape, including widely deployed and hard to access connected objects, mission critical industrial systems where downtime is costly, smart cards with long renewal cycles, and legacy equipment with limited or no update capabilities.
The risk is clear: a lasting gap could emerge between traditional IT environments, which will progressively migrate to PQC, and embedded IoT systems, which may remain vulnerable for a much longer period. Organizations must anticipate this challenge now by embedding PQC compatibility requirements into their specifications for all new deployments of embedded and connected equipment.
A Nuanced Market Outlook
The market has now clearly acknowledged that the post-quantum transition will necessarily begin with a systematic inventory phase and a comprehensive risk assessment, a realization that has reshaped the structure of the ecosystem. This growing awareness is reflected in several encouraging developments: the proliferation of specialized solutions for mapping cryptographic assets; the first official certifications for PQC compatible security modules, confirming their readiness for operational deployment; and the maturity of opensource libraries, now widely supported by the industry. Migration support tools further complement this landscape. In parallel, perimeter security approaches already make it possible to protect sensitive data flows without waiting for a full system overhaul.
However, this momentum continues to face persistent challenges. Delays in the development of suitable hardware – particularly for IoT and embedded systems – remain a major obstacle, with a still limited availability of low power, PQC compatible processors. Certifications, while promising, remain limited in number and cover only part of the available technological spectrum. Finally, inventory tools, despite becoming increasingly sophisticated, have yet to fully demonstrate their ability to effectively address the complexity and heterogeneity of large enterprise IT environments.
As a result, while the market has clearly oriented its efforts toward inventory and risk analysis as essential prerequisites for migration, technological and industrial challenges continue to slow largescale adoption.


