In 2025, ransomware attacks remained a persistent threat and increasingly targeted backup systems (21% of attacks targeted backups in 2021, compared with 90% in 2025 [1] ). Protecting backups, now also subject to strengthened regulatory requirements such as NIS 2, has therefore become a top priority in addressing this threat.
This article presents four complementary approaches to strengthening end-to-end backup security:
- Continuously ensuring the availability of usable backups
- Strengthening the security of the backup infrastructure against attacker takeover
- Protecting backups against logical destruction
- Identifying residual risks in light of the measures implemented
This article is published in two parts: the first focuses on approaches 1 and 2, followed by a second publication covering approaches 3 and 4.
The recommendations presented do not replace those set out in ANSSI guidelines, which define the fundamental principles of backup [2] practices.
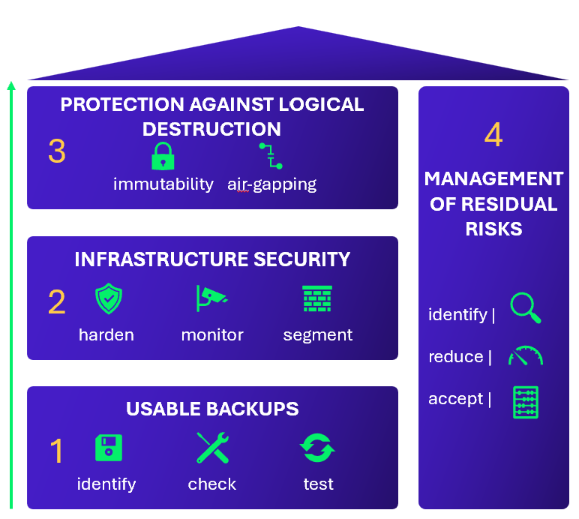
Figure 1: Strengthening Backup Security Through Four Approaches
1. Continuously ensuring the availability of usable backups
To guarantee the availability of usable backups, it is essential to apply fundamental best practices.
Ensuring backup completeness and consistency
In the context of a ransomware attack, the primary objective of backups is to provide a reliable data source enabling the reconstruction of the information system. Backups are truly effective only if they contain all the elements required for full recovery. This notably includes businesscritical data, configurations of business applications and systems, installation sources, as well as critical operational data such as password vaults, licenses, and operational documentation.
Backup completeness alone is not sufficient. The need for data consistency points across backups originating from different sources (e.g., a document management system (DMS) database and its associated files) must also be taken into account. Conducting a preliminary analysis helps facilitate data resynchronization across different repositories during the recovery phase.
In addition, it is necessary to maintain backups of the infrastructure itself to enable identical reconstruction. These backups must include the backup catalog, software installation sources, encryption keys, and all other required secrets. A copy of configuration parameters should be stored in a separate location, such as an offline environment, distinct from the primary infrastructure, in order to limit the risk of a shared compromise.
According to the Cyber Benchmark conducted by Wavestone across more than 170 assessed organizations, approximately 90% of the organizations observed perform regular data backups.
Among organizations that perform regular backups:
- Approximately 65% conduct restoration tests
- Approximately 20% perform business data consistency checks
In this context, various controls must be defined and implemented on a regular basis.
Testing Backup Reliability Through Regular Controls
A first level of control aims to ensure that backups are effectively performed and remain usable. This can be based on the application of daily verification procedures relying on evidence such as reports, logs, and alerts. These checks may be manual or (semi) automated. However, an additional human review remains necessary to ensure that indicators and alerts are not misleading, particularly in the event that monitoring and control mechanisms have been compromised or disabled by an attacker.
This first level also includes periodic restoration tests, carried out on representative scopes, in order to verify, where possible with the involvement of application or business subject-matter experts, the integrity and completeness of the data required for business recovery.
The second level consists in ensuring that first-level checks are properly applied. It relies on independent controls or formalized processes. Dashboards may be used to centralize confidence-level indicators by correlating the results of daily operational checks with restoration test outcomes.
Once the reliability of backups has been established, restoration processes should be optimized by regularly testing them and ensuring their effectiveness.
Industrializing Restoration Processes to Optimize Recovery Time in the Event of a Compromise
To reduce recovery time following a compromise, it is essential to industrialize restoration processes at scale in order to support mass recoveries. This requires preparing these processes in advance, testing them regularly, and adapting them to different destruction scenarios.
As the restoration phase of an information system may extend over several weeks, or even several months, it is necessary to increase backup retention periods for the data to be restored, in order to prevent their loss through overwriting or premature deletion.
Restoration processes must also include mechanisms to rapidly assess the state of backedup data by identifying, based on indicators of compromise, data that has been compromised, modified, or corrupted, so as to effectively target the appropriate restoration points.
Integrating the Risk of Backup Compromise into the Restoration Strategy
To ensure reliable recovery following a compromise, it is essential to account, within the overall restoration strategy, for the risk of alteration or manipulation of backedup data. This involves addressing the risk of data alteration or manipulation occurring upstream of backup processing by the backup agent, for example:
- Being able to rely on full backups created prior to the attacker’s intrusion, as identified during the initial investigations. In such cases, the backedup data can be considered uncompromised and used to rebuild systems and applications.
When restoring unaltered application or system components that are not reinstalled from trusted sources, the restoration process must also include the application of security patches and hardening measures to prevent any subsequent compromise.
The backup process alone cannot prevent potential data compromise before the data is handed over to it. Depending on the context, additional measures may be implemented, such as:
- Protecting data integrity through system-level mechanisms and/or cryptographic means;
- Detecting data alteration through application-level validation, monitoring of “canary files” data, or the use of an EDR (Endpoint Detection and Response) solution.
These topics must be addressed in addition to backup protection measures.
Extending Backup and Restoration Best Practices to Cloud Environments
Finally, the backup rules defined for onpremises environments must be replicated and adapted to cloud environments.
According to the Cyber Benchmark conducted by Wavestone, approximately 25% of the organizations observed have a regularly reviewed and updated backup policy covering both onpremises and cloud environments.
In addition, around 29% of organizations externalize a backup of their cloud data to another region or to an onpremises environment, ensuring resilience against cyberattacks and regularly testing this process.
Beyond the usability of backups, securing the infrastructure that hosts them represents an equally critical challenge, one that is sometimes insufficiently addressed.
2. Strengthening the security of the backup infrastructure against attacker takeover
Before considering more advanced mechanisms, it is important to recall that effective backup protection first relies on best practices for securing the backup infrastructure, notably those documented by ANSSI3. A compromise of this infrastructure could indeed result in the alteration of backups (encryption, destruction, etc.).
Ensuring Defense in Depth for the Backup Infrastructure
These best practices include segregating production and backup environments, using dedicated administrative accounts, and hardening infrastructure components, particularly through the application of ANSSI hardening guides applicable to Windows, Linux, and other systems. They also apply to backup agents, which may constitute a propagation vector toward production systems.
In addition to hardening measures, the backup infrastructure must be subject to both technical and cybersecurity monitoring.
Implementing technical and cyber monitoring of backup infrastructures
Technical monitoring of backup infrastructures helps ensure their proper operation and detect any anomalies. The effective handling of detected anomalies must be regularly reviewed.
Cybersecurity monitoring of the backup infrastructure relies on appropriate logging and traffic analysis. It must be capable of detecting the main attack techniques observed in the wild.
Maintaining Threat Intelligence Focused on Backup Systems
Threat intelligence specifically targeting backup systems must be maintained, beyond the technical vulnerability monitoring performed as part of maintaining the backup infrastructure in a secure operating condition. This threat intelligence should cover attack techniques and tactics used against backup infrastructures, in order to anticipate potential attacks and adapt protection, detection, and response capabilities accordingly.
Despite the measures implemented to prevent the compromise of backup infrastructures, the risk of logical destruction remains and must be anticipated.
Reference
[1] Wavestone, CERT
[2] ANSSI, Sauvegarde des systèmes d’information
[3] ANSSI, Sauvegarde des systèmes d’information


