Electric mobility is experiencing rapid growth in France and across Europe: in January 2026, registrations of fully electric vehicles in France increased by more than 50% compared with January 2025, bringing their market share to nearly one third of total vehicle sales. This trajectory confirms a structural transformation of the automotive sector, which appears to be entering a phase of massive electrification, particularly for light-duty vehicles. This momentum is fully aligned with the orientations set out in France’s Multiannual Energy Program (PPE), which translates national ambitions for the energy transition into operational targets. As such, the growth of electric vehicles can no longer be considered short-term, but rather as a trajectory set to strengthen further.
This trajectory, however, relies on the availability of a dense, reliable, and properly dimensioned charging network across the entire territory. Whether for public charging (motorways, public roads, shopping centers) or private charging (homes, businesses), this infrastructure forms the backbone of the electric mobility ecosystem. At the heart of this ecosystem, Charging Point Operators (CPOs) play a structuring role, being responsible for the installation, operation, and maintenance of charging stations.
Cyber risk is now emerging as a major threat to charging infrastructures, in a context where electrical networks are increasingly targeted by cybercriminal groups and state-sponsored actors12. For CPOs, this reality is a game changer: mastering cyber risk becomes a prerequisite for service reliability and ecosystem protection. As charging networks expand and grow more complex, cybersecurity challenges become central: data protection, service continuity, securing financial flows, and managing third‑party risks.
This article is part of a series of three papers exploring three structuring challenges faced by electric mobility stakeholders, with the aim of analyzing their implications from a cybersecurity perspective.
Rethinking charging infrastructure: balancing operational requirements and emerging cyber constraints
In the context of strong growth combined with the gradual structuring of the market, CPOs are facing a demanding economic equation. The deployment of charging infrastructures requires significant upfront investments – land acquisition, grid connection, purchase and installation of charging points, supervision, and maintenance – while utilization rates remain heterogeneous across regions and site typologies. Added to this are the volatility of electricity prices, increasing competitive pressure, and the rapid evolution of technological standards, which require regular upgrades.
As public subsidies tend to be streamlined and investors increasingly expect clearer profitability trajectories, optimizing the economic performance of assets becomes imperative. Maximizing availability rates, fine‑tuning operating costs, improving utilization levels, and diversifying revenue streams are no longer secondary levers, but essential conditions for the long‑term sustainability of CPOs’ business models.
Charging infrastructures, as designed today, illustrated in Figure 1, generally rely on static power control managed by a central supervision system, the Charging Point Management System (CPMS). This operating model does not allow, or significantly limits, the CPO’s ability to adapt power distribution in real time to usage patterns and site-specific constraints.
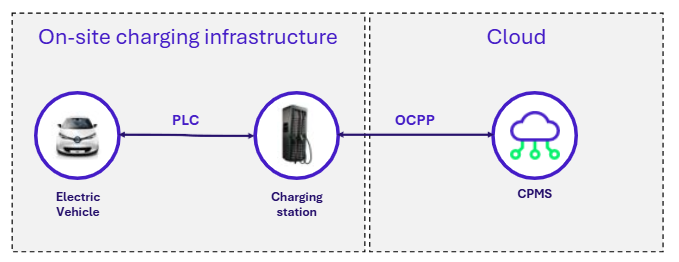 Figure 1: Architecture of a conventional charging infrastructure
Figure 1: Architecture of a conventional charging infrastructure
Therefore, several optimization levers can be implemented.
First, it is possible to enhance the site’s energy flexibility, particularly to support fast charging without having to oversize the grid connection. To achieve this, the deployment of a Battery Energy Storage System (BESS) proves to be an effective solution: this stationary battery storage acts as a buffer, capable of storing energy when it is available and releasing it during peak demand, thereby improving the site’s stability and resilience.
The next step consists in integrating local, low‑carbon energy production directly at charging sites, making it available for immediate use or storage through the addition of photovoltaic systems. Solar panels, installed on rooftops or canopies, provide this renewable generation layer. Their effectiveness, however, relies on their integration with appropriate control and storage systems, ensuring the environmental coherence of electric mobility.
Finally, to enable the proper integration of these energy production and storage assets at charging sites, a global control system has emerged: the Energy Management System (EMS). This system supervises and adjusts energy flows on site in real time, aligning them with demand, local constraints, and grid connection agreements. It controls power distribution, anticipates variable charging demand, and maximizes the use of local energy production, thereby transforming a conventional electrical installation into a dynamic and intelligent system.
Thanks to intelligent energy management via an EMS, battery storage, and the integration of solar generation, this architecture (illustrated in Figure 2) enables performance optimization while keeping costs under control and thus represents a key step towards the next phase of the energy transition.
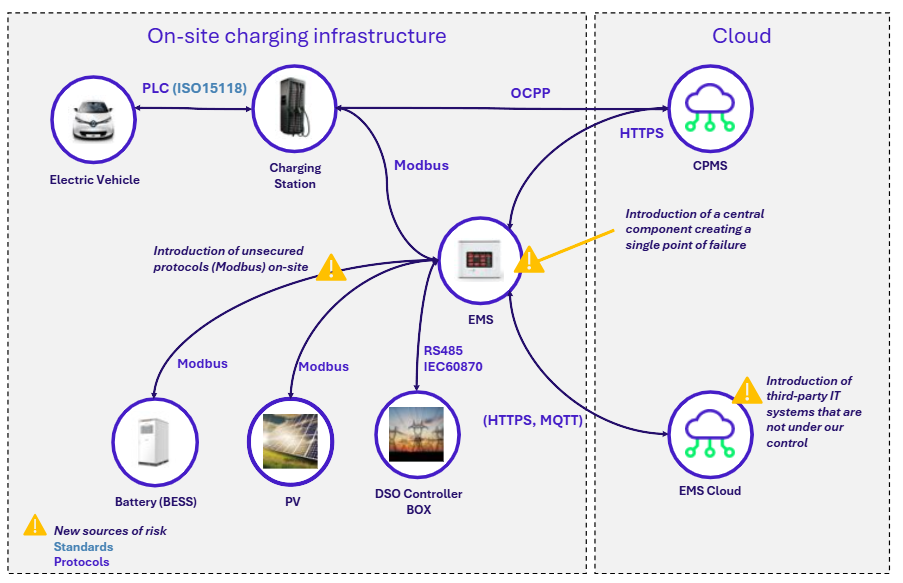
Figure 2: Architecture of a next-generation charging infrastructure
In the remainder of this article, we will focus on three new sources of cybersecurity risk introduced by the integration of Energy Management Systems (EMS) into CPOs’ charging infrastructures.
The EMS: an optimization lever that has become a critical risk point
EMS have become a key component of charging infrastructures, enabling CPOs to finely optimize power management and charging strategies. This central role makes EMS a critical point in terms of cybersecurity – their compromise can result in major operational impacts for a CPO:
- Unavailability of a part of the charging stations.
- Degradation of energy optimization, resulting in direct financial impacts.
- Load imbalances that may lead to service limitations or outages at site level.
Beyond these incident scenarios, the introduction of EMS also fundamentally reshapes the risk landscape to which charging infrastructures are exposed.
Increased reliance on third‑party infrastructures
The deployment of EMS solutions is most often based on turnkey offerings, combined with vendor‑operated management platforms hosted in cloud environments. These platforms enable CPOs to centrally manage their entire EMS fleet and support a range of use cases, including optimization of available power, performance monitoring, and remote control of charging strategies.
This architecture, however, introduces a direct dependency on third‑party infrastructures that lie outside the CPO’s perimeter of control. As a result, it expands the attack surface and increases CPOs’ exposure to supply‑chain‑related risks.
This issue is further compounded by the fact that these vendors are often small, highly specialized players whose level of cybersecurity maturity can be heterogeneous. A compromise of these platforms may therefore lead to widespread impacts, potentially resulting in the unavailability of a significant share of the EMS fleet operated by a CPO and, by extension, a risk of charging station outages.
In addition, the compromise of EMS cloud platforms may also lead to breaches of data confidentiality, as it could enable an attacker to collect sensitive operational information, which could notably be exploited for espionage purposes, including:
- Detailed mapping of charging sites and deployed energy assets.
- Energy management strategies, revealing the optimization logics implemented by the CPO.
- Consumption and power data across the CPO’s entire portfolio of sites.
Local communications relying on weakly secured protocols
These new architectures also extend the attack surface at the local network level, particularly through communications with energy-related equipment, which still largely rely on weakly secured industrial protocols.
Unlike exchanges between supervision systems (CPMS) and charging stations, which benefit from the standardization provided by OCPP, communications between the EMS and other components (BESS, charging points, etc.) still predominantly rely on Modbus.
Originally designed for closed industrial environments, this protocol does not natively implement security mechanisms such as authentication or encryption. In practice, each EMS vendor deploys its own protective measures, resulting in heterogeneous security levels. For CPOs, this diversity complicates the securing of the fleet and may introduce new exploitable weak points within the local network.
Levers to secure next‑generation charging infrastructure
Securing next‑generation charging infrastructures relies on a structured approach that makes it possible to reconcile operational performance with effective cybersecurity risk management.
Ensuring the resilience of charging architecture
The evolution of charging infrastructures introduces a single point of failure for CPOs: the EMS. To address this risk, it is necessary to design resilient architectures capable of maintaining continuity even in the event of an EMS failure. This can notably be achieved through:
- The implementation of monitoring and alerting mechanisms, enabling rapid detection of EMS failures and activation of fallback mechanisms.
- The deployment of degraded operating modes, allowing charging stations to continue operating even in the event of EMS unavailability.
- The definition of business continuity and disaster recovery strategies that explicitly include EMS failure scenarios.
Securing dependencies on unmanaged third–party infrastructures
The evolution of charging infrastructure architectures requires CPOs to address both supply‑chain‑related risks and risks inherent to the interconnection between the CPMS and EMS vendors’ cloud infrastructures.
To reduce supply‑chain risks, CPOs must implement robust vendor qualification processes, including in particular:
- Assessment of the vendor’s cybersecurity maturity level.
- Evaluation of product security, notably through penetration testing.
- Contractual governance of supplier relationships, including, where appropriate, the implementation of Security Assurance Plans (SAPs).
Beyond supply‑chain risk management, CPOs must also account for the risks introduced by the interconnection of their infrastructure with EMS vendors’ environments (EMS cloud). Securing these interconnections requires a strong control of data flows between the CPO infrastructure and these external environments. This can be achieved through three main levers:
- Implementing traffic filtering and control mechanisms between the local charging infrastructure network and external networks, to restrict communications strictly to legitimate third‑party infrastructures.
- Formalizing secure architectural standards and ensuring their effective implementation during EMS deployment in the field, guaranteeing a consistent application of cybersecurity best practices.
- Implementing isolation mechanisms to contain potential EMS cloud failures and prevent their propagation across the entire charging infrastructure fleet.
Securing communications relying on industrial protocols
Communications between EMS and energy‑related equipment, particularly BESS, still largely rely on industrial protocols such as Modbus, which do not provide native security mechanisms. In this context, securing these exchanges cannot rely on the protocols themselves, but must instead be addressed at the infrastructure architecture level.
This notably involves:
- Implementing strict network segmentation within the local network, isolating EMS, BESS, and other components to limit exposure surfaces.
- Applying fine‑grained control over communications by locally restricting data flows to strictly necessary exchanges (filtering, whitelisting, limitation of authorized commands).
- Deploying communication monitoring mechanisms to detect abnormal or unauthorized behavior.
Establishing a structured cybersecurity governance
To address the diversity of components and infrastructures operated across their charging networks, it is essential for CPOs to structure their environment around clear governance, including in particular:
- Clarification of cyber roles and responsibilities across the entire value chain (CPOs, suppliers, service providers, etc.).
- Definition of security standards applicable to all projects and suppliers, ensuring overall architectural consistency.
By combining rigorous supplier risk management, a solid governance framework, and strict control of data flows, CPOs can fully leverage the operational gains offered by EMS while securing their infrastructure in a sustainable manner.
Optimizing without compromising: the challenge of charging infrastructure
To conclude, the rise of Energy Management Systems (EMS) is profoundly transforming charging infrastructures, providing essential optimization levers while also introducing new cybersecurity risks. For CPOs, the challenge is no longer limited to deploying these solutions but extends to securing them within a comprehensive approach that encompasses supplier risk management, the definition of secure architectures, and the establishment of structured cybersecurity governance. In this context, cybersecurity is now emerging as a prerequisite for the sustainable performance of charging infrastructures.


